Uncle SCAM Wants You….
Every year 15 million Americans become victim to identity theft. That is insane and infuriating to say the least. It makes my blood boil when I think about how a human being can prey on another human being and take what does not belong to them. There are SO many ways to get duped by these cold blooded and heartless beings. Some of them are almost genius and I can tell you that I would not make a good scammer as apparently I am not nearly smart enough to come up with this stuff! I often read or hear about these things and think to myself “how do they think of this stuff?”. I have nearly been duped tho, and I’ll share a personal story about it…and how I totally should have known better…a little later in this post, but what is even more disheartening is that they prey on the elderly. They rely on the fact that the elderly aren’t of the “technology age” and it is easy to fool and confuse them. Honestly you don’t even have to be elderly to fall victim because some of these scammers are very good at what they do.
What we are going to talk about in this post is what to look for and how to recognize a scam as well as how to help protect yourself from letting them access your personal sensitive information.
To keep this read from being super long, I’m only addressing Phising and how to protect yourself on your mobile devices (phones, tablets, laptops). I will address protecting yourself at home in another post.
To start, let’s explore phishing.
Phishing
So what is “phishing”? Well, it’s basically like fishing…..a scammer casts a line with some sort of bait and waits for you to bite. Once you nibble, they got you hook, line and sinker! To get a technical definition on phishing, let’s see what our friend Wikipedia has to say:
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker[1] or to deploy malicious software on the victim's infrastructure like ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim.[2] As of 2020, phishing is by far the most common attack performed by cybercriminals, with the FBI's Internet Crime Complaint Centre recording over twice as many incidents of phishing than any other type of computer crime.[3] Phishing awareness is becoming essential at home and at the work place. For instance, from 2017 to 2020, phishing attacks have increased from 72 to 86% among businesses.[9]
I’m sure that by now, most everyone has had some sort of experience with a phishing scam. It would be hard not to in this day and age. They can come through many avenues and they can be relentless. The following are just some examples of different types of phishing scams:
Survey Scams - They catch your attention by sending an email asking you to take a survey about something you have shown interest in…rescuing animals, saving the rainforest or any other good cause. They may even promise monetary or some other form of compensation for taking the survey just to entice you a little more. Once you’ve clicked on the link for the survey…boom…spyware or malware is installed on your computer and from there, the scammers can see your every move, like your bank account, health records and any other sites you visit.
PayPal or Other Payment App Scams - I can remember when PayPal was literally the only payment app around, but now we have a small army of them available. The scammers will send an email saying that your account will be deactivated if you don’t respond immediately or they say that there is a security issue with your account and they ask you to click the link to log into your account and verify your information. Again, once you’ve clicked that link, you’ve opened that door and they can track your moves. The link doesn’t take you to the actual payment app but instead takes you to their site, which very closely mimics the real site and as you type in your information, they are licking their chops! Now they have your bank information and guess where they are going next!
Your Computer Is Infected Alert - These emails aim to make you think that they have miraculously discovered a virus on your computer and all that you need to do is download a protection service or an application that will take care of the virus. In reality, the link they are providing for the protection actually contains the malware and it infects your computer and they then have access to all of your information.
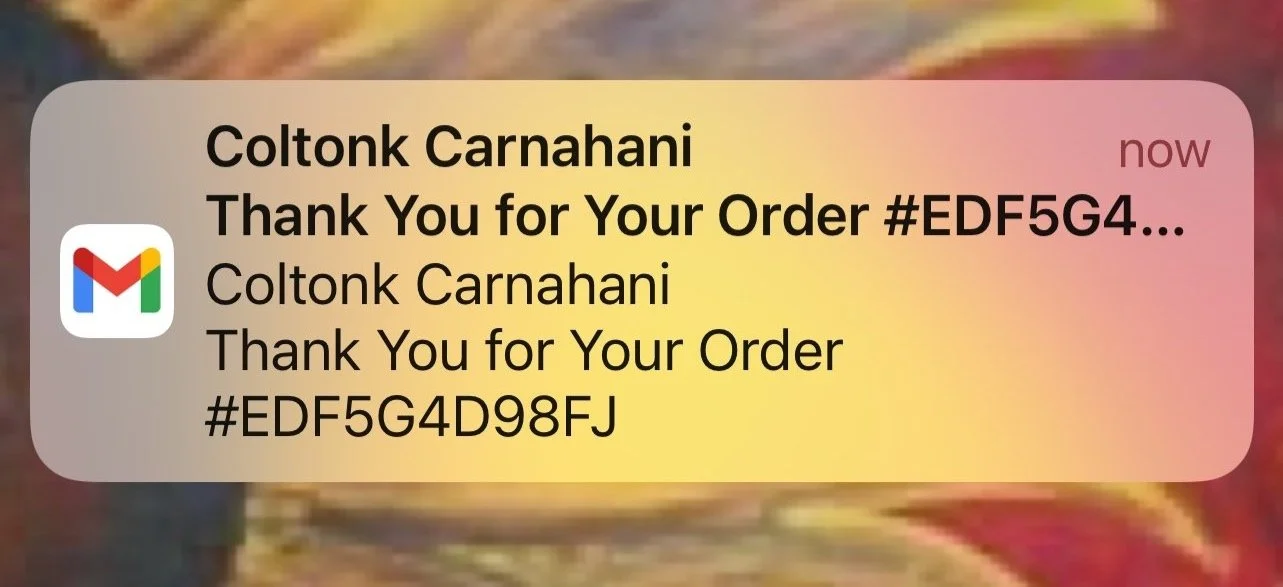
Order Confirmation - Just like in the picture below (which happens to be an actual screen shot from my phone), you get an email with what looks like an order confirmation. Your first impulse is to think….or say out loud if you tend to talk to yourself like I do….”I didn’t order anything” and panic because you fear that something is being charged to a credit or debit card. The bait here is that panic, and they want you to open the email and click on the order confirmation link, or a link to cancel the order. Once you do, they will most likely want you to put in card or account information so that they can “refund” you but….and you know where this is going….there was no order, there is no refund and now they have the information that they want in order to gain access to your accounts and do a little shopping of their own. The best thing you can do is delete the unopened email. Keep good records of any orders you do place on line so that you know exactly what, when and from whom you have ordered, that way there will be no confusion. Any good and reputable online store will provide you with all of your order information and a confirmation immediately once you’ve hit the “placed order” button as well as an immediate email with all of the same information. Be vigilant, be aware and keep good records.
Phishing email.
Now let’s talk about how your mobile devices. How easy has our lives become by having a phone or tablet that we can carry with us every where? Not only can we call someone regardless of where we are or where they are, but our phones hold soooooo much information and it’s always right at our fingertips! The issue with all of this is that the multitude of conveniences that mobile phones afford us can also be detrimental to us. Many people, myself included, have a mobile banking app or what about those nifty payment apps like Venmo and Cash App. All of these apps leave the door wide open to hackers and scammers. By taking some precautions, you can keep all of those handy apps, while protecting your valuable information from predators. Here are some tips to help keep you safe:
Lock Your Phone Screen - I see so many people who get off a phone call or text, or even after being on other apps such as social media, or googling directions or suggestions for food or shopping…whatever it may be….they don’t lock their screen and just put their phone back in their pocket or lay it down. This can be dangerous because someone could grab your phone without you noticing and they have free access to everything! ALWAYS lock your phone screen when you finish using it. It’s also VERY important to make sure you have a passcode or facial recognition set up to open your phone. I know, it can be a pain to take the time to type in a passcode or wait for the facial recognition to open the phone, but is that few seconds worth letting a predator gain access to your world? NO…it’s as simple as that.
Charge Cautiously - Another snazzy thing about mobile phones is that you can charge them anywhere there is an outlet! How many times have you plugged your phone in while at a restaurant, while taking a break at the shopping mall or while waiting to board your flight at the airport? This can be dangerous! I’m telling you, thieves think of EVERYTHING and compromising outlets are another avenue for them to gain access to your phone. It’s insane to think that something so innocent as charging your phone in public could cause your information to be accessed, but it’s the reality of the world we live in today. We continually have to try to be one step ahead to protect ourselves. So next time you are going to be out for a while, be vigilant about charging your device before you go!
Do the Updates - Ugh I know, it seems like there are always software updates and you aren’t able to use your device while it’s updating….so frustrating. BUT…by keeping your device’s software up to date, it can limit malware malfunction. Malware or “malicious software” is a term that describes any malicious program or code that is harmful to operating systems. Take the time to do the updates. If you can’t be without your device during the day, then let it update overnight when you are not using it.
Bluetooth, WiFi & Hot Spots - These connection options are a wide open invitation for hackers. Again, it’s mind boggling to me but these lazy people are smarter than smart. Hackers will use specialized software to detect which nearby devices are equipped with bluetooth and they can also see what networks your device has connected to….which is key because most devices now treat the networks that you most frequently connect to as “trusted” and it will automatically connect to them when you are at or near that network. The hackers will attempt to replicate those trusted networks and trick your device into connecting. Once that happens, they have access to all of the same things you do on that device. Hackers can even intercept or redirect calls and texts and what’s most scary is that they can watch and listen to everything you do and say…in real time! Keep your bluetooth turned off when you are not using it and when you are, be cautious about the environment you are in. Busy public places are prime opportunities for the cybercriminals to strike. If you use the hotspot on your phone or other devices, make sure it is encrypted and password secured. If not, anyone near you can hop on your hotspot and do all of the same damage as through bluetooth access. WiFi is yet another way for hackers to access your device. We love public WiFi right? It’s free and you’re not using data so it’s got to be good right? Not always! There are various ways that hackers can use public WiFi to hack your device. For the sake of not making this read any longer than it already is, I’m not going to outline all of the ways, however, I will tell you that using a VPN (virtual private network) will protect you. A VPN is a service that you pay for and install on your devices that then scrambles all of your private information and without the correct decryption key, hackers are unable to read it. There are free VPN services, but as with just about everything else most that say they are free are a scam. You get what you pay for….so don’t be cheap, use a VPN service that has a fee and you’re more likely to be protected. Do your research, make sure the service you intend to go with is legit or else you’re just jumping from the pan into the fire!
So, in a nutshell these are some things you can watch for to help protect your personal sensitive information and not end up victim to one of those slimy cybercriminals. The web has a plethora of additional information and I highly encourage you to check it out! We all work too hard for what we have, we have to make sure that no one is taking it right out from under our noses. Take the time to safeguard your information, your kids’ information, and be sure to share what you’ve learned here and from any other sources with family and friends.